Since June 2022, Maltego has launched a new social media campaign that provides Maltego users and investigators with cheat sheets showing how to best use our Hub items for certain workflows. Check out the Investigator Toolkit August roundup in this article!
Presented to you by Maltego, the Investigator Toolkit series showcases each Maltego Transform Hub item with a sample workflow applicable to certain types of investigations. This series aims to help you quickly learn how to include a particular Hub item in your existing workflows.
Where to Find the Investigator Toolkit? 🔗︎
You can find the Investigator Toolkit series on our Twitter and LinkedIn channels, with the hashtags #MaltegoMonday and #InvestigatorToolkit. Every Monday, each Investigator Toolkit post comes with a workflow cheat sheet as well as a blog article or webinar as an additional demonstration.
All Previous Investigator Toolkit Roundups 🔗︎
In August, we featured the following five Hub items and their use cases in the Investigator Toolkit series:
Let’s dive straight into how to use these Hub items for threat intelligence, social media investigations, or website mapping and backtracking!
Intel 471: Threat Actor Identification 🔗︎

To identify certain threat actors and their affiliates, you can run Intel 471 Transforms on a Phrase Entity to extract related reports, dark web forum threads, and aliases of post authors. See how we map out affiliates of DarkSide ransomeware using Intel 471.
ShadowDragon SocialNet: SOCMINT Targeting Investigation 🔗︎
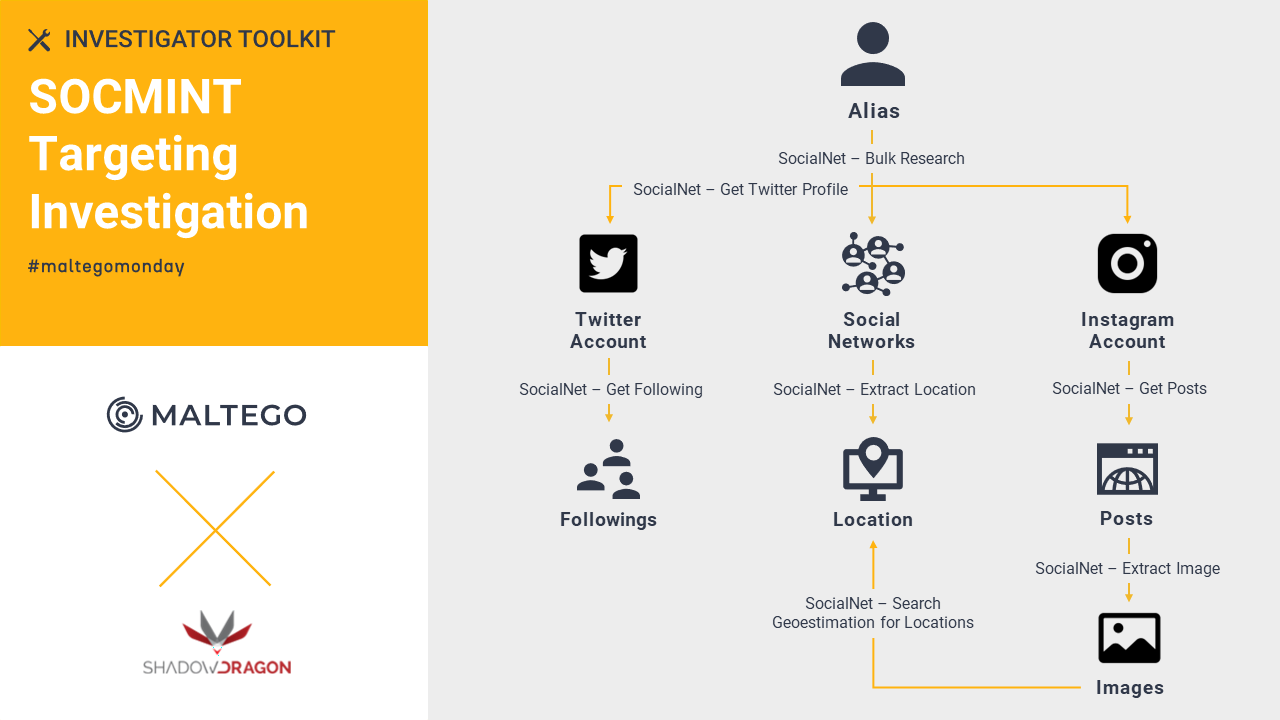
You can easily pull data from various social media platforms, visualize the connections, and acquire actionable intelligence using ShadowDragon SocialNet Transforms in Maltego. Watch our joint webinar with ShadowDragon about how to investigate illicit communities.
Scamadviser: Scam Websites Mapping 🔗︎

With Scamadviser, you can easily identify risky or fake crypto- and shopping websites, map out scam networks, and combat currently rising online scams. Watch our joint webinar with Scamadviser to see how we identify fake shopping websites and its scam networks.
Farsight DNSDB: Archived Website Backtracking 🔗︎
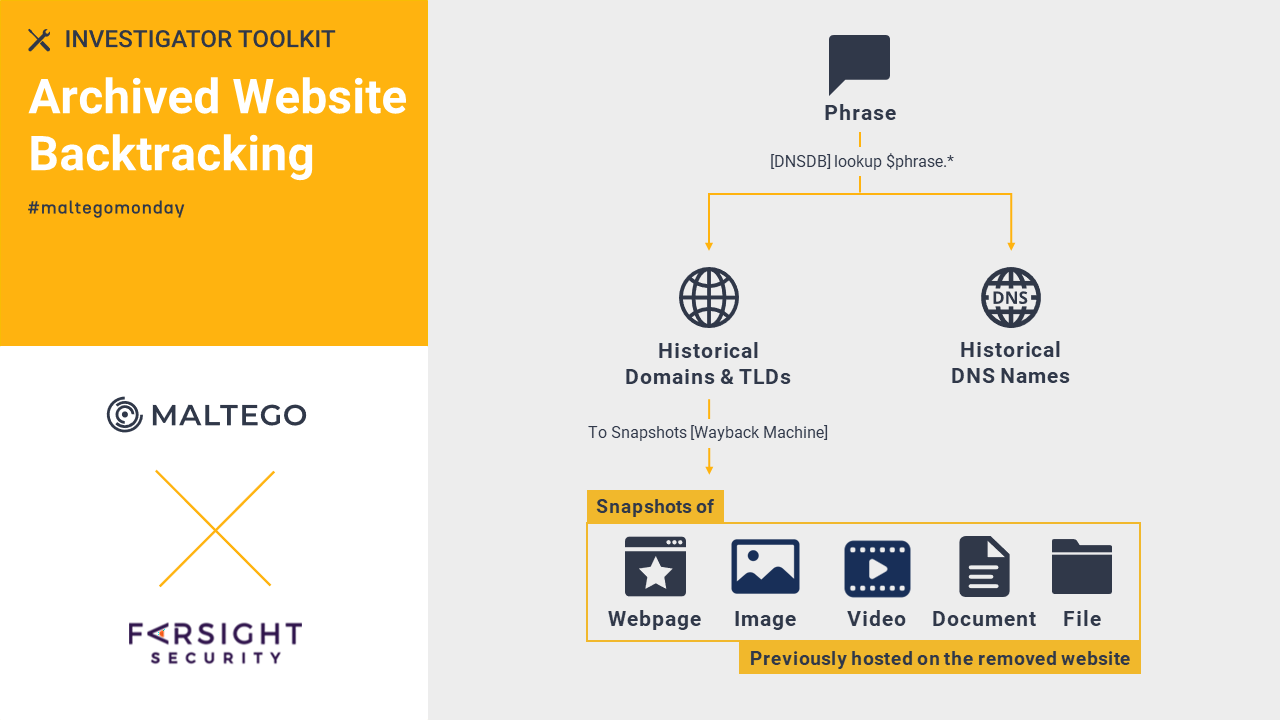
To backtrack historical activities of a removed website, you can retrieve snapshots and content previously located on the website with the power of Farsight DNSDB and Wayback Machine Transforms. See how we explore archived content from domains and gather relevant information of amaqagency.

To identify and understand the network of criminal posts, forums, communities, and users, simply plug in and run Flashpoint Transforms. Read how we use Flashpoint to scrape the GozNym botnet operations across Russian-language cybercrime forums.
In the following months, we will continue digging into different Hub items available through Maltego and providing best practice tips to investigators.
Follow us on Twitter and LinkedIn now, so that you won’t miss upcoming Monday tips!
Happy Investigating!